Top 5 Cloud Security Risks for Startups
A deep dive into the top five cloud security risks encountered by early stage startups.
According to Snyk, the number of organisations that encountered a significant security incident related to their cloud infrastructure was 80%. In fact, they claim that a whopping 89% of the affected businesses were startups! Cloud security incidents can lead to severe consequences like penalties for failing audits, regulatory compliance violations, abuse of cloud resources, loss of business due to system disruption or downtime, and reputational loss. And, in a post-ZIRP world where being default alive is the most important thing for startups, an incident stemming from poor security hygiene can put you completely out of business.
As part of a multi-part series on cloud security, we'll delve into the top five cloud security risks that I've seen early stage startups encounter, and discuss some of the resulting consequences. In subsequent posts, I'll dive into each risk and explore mitigation techniques and best practices. The controls will mostly be cloud vendor-agnostic but, where relevant, I'll highlight AWS or Google Cloud-specific controls.
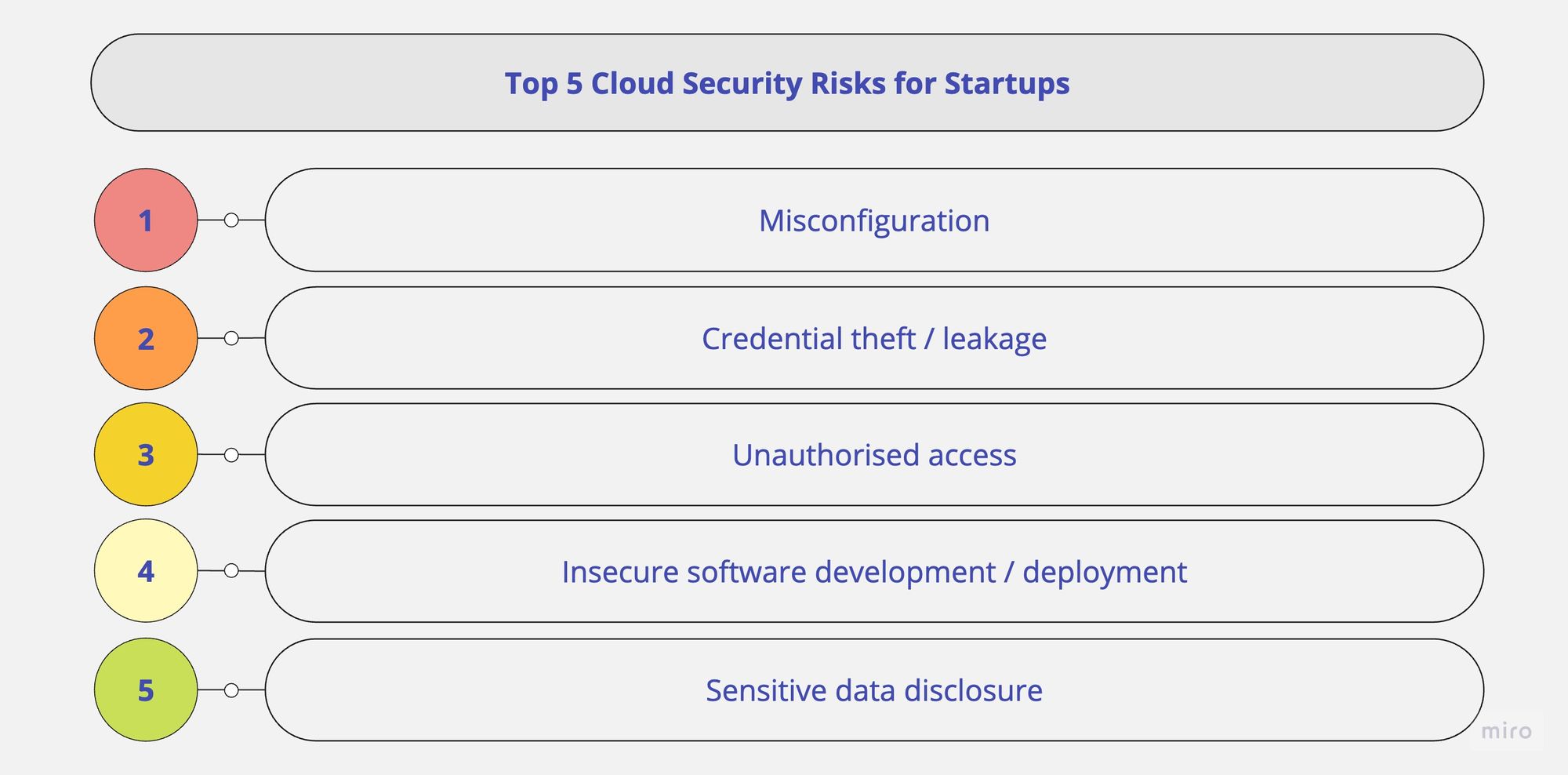
Misconfiguration
Cloud platform or resource misconfiguration is the leading cause of cloud security incidents. Whether it's an improperly configured storage bucket, an open network firewall port, or an overlooked access control setting, the consequences can be severe. According to Radware, 69% of organisations experienced data breaches or exposures due to multi-cloud misconfigurations. Generally, the main causes of misconfiguration in cloud environments are:
- Unclear or unassigned platform security responsibilities
- Lack of awareness/education about common misconfigurations
- Insecure platform or service defaults
- No real-time visibility into misconfigurations or configuration changes
- Human errors resulting from a lack of automation
Credential theft/leakage
Credential compromise, whether via theft or leakage, is probably the second-most common risk facing startups. When unauthorised individuals or services get access to highly privileged credentials, they can easily manipulate your cloud resources, steal sensitive data, or disrupt your operations. Generally, the main causes of credential compromise in cloud environments are:
- Use of highly privileged accounts (e.g. super admin) for daily operational tasks
- Lack of strong multi-factor authentication schemes (e.g. none or SMS OTP)
- Lack of single sign-on (SSO) - this one is hard because of sso.tax
- Long-lived credentials or access tokens
- Service account credential (key) abuse/compromise
- SSH key abuse/compromise
Unauthorised access
According to Ermetic, 83% of organisations have experienced at least one cloud data breach related to unauthorised or misconfigured access. While the previous risk focused on identity and authentication, this one highlights authorisation risk. Once an attacker has access to credentials, the extent of damage they can do depends on their level of access to resources in your organisation (aka lateral movement and blast radius). This risk does not focus on external access only though, as inadvertent errors/mistakes by well-meaning employees, as well as insider abuse, also play a significant role. Generally, the main causes of unauthorised access in cloud environments are:
- No segregation of duties (e.g. access to encryption keys and data)
- Homegrown authorisation or access control schemes
- No multi-party authorisation for sensitive actions
- Over-granted permissions, no periodic review
- Publicly exposed resources, sometimes by default
- Bastion host (or jump host) compromise
- Lateral movement post-initial compromise
Insecure software development/deployment
While not exclusive to cloud environments, the software development and deployment process can introduce vulnerabilities that attackers can exploit to breach your organisation. Addressing security early, i.e. shifting left, reduces the cost and effort of maintaining the software, leading to a more resilient security posture. Generally, a few reasons for insecure software development and deployment are:
- Insecure coding practices (see Secure Software Development Framework)
- Vulnerable base images for virtual machine instances, Kubernetes nodes or container images
- Web application vulnerabilities (e.g. OWASP Top 10)
- Open-source and software supply chain vulnerabilities
- Leaked secrets (e.g. API keys, certificates, database passwords)
- Distributed Denial of Service (DDoS) attacks; a variation, Economic Denial of Service (EDoS) attacks, target your billing/wallet instead
Sensitive data disclosure
Startups often collect and process sensitive customer data, including personally identifiable information (PII). Inadequate data protection measures can lead to its theft or unauthorised disclosure, resulting in significant reputational damage, loss of business and legal ramifications. According to IBM, the average cost of a data breach for organisations using a private cloud is $4.24M, while for those using the public cloud is just over $5M. After the launch of Europe's GDPR, more countries worldwide have started adopting and publishing their own data protection regimes, thereby increasing the cost of compliance for startups operating globally. Generally, the main causes of sensitive data disclosure in cloud environments are:
- Limited visibility into sensitive data (i.e. no data discovery and classification)
- Missing data governance considerations
- Sensitive data (e.g. PII/PHI) theft or accidental leakage
- Insecure data sharing/exchange with business partners or vendors
- Unauthorised data access, usually stemming from over-granted permissions
If you found this post useful, feel free to read others in this series:
- Top 5 Cloud Security Risks for Startups (this post)
- Addressing Cloud Security Risks: Part 1 - Misconfiguration
- Addressing Cloud Security Risks: Part 2 - Credential Theft/Leakage
- Addressing Cloud Security Risks: Part 3 - Unauthorised Access
- Addressing Cloud Security Risks: Part 4 - Insecure Software Development & Deployment (coming soon)
- Addressing Cloud Security Risks: Part 5 - Sensitive Data Disclosure (coming soon)