What are Canary Tokens?
A brief on canary tokens, an easy way to discover network and system intrusions.
As cruel as it may seem, canaries have played a critical role in mining history, used by miners to detect dangerous levels of toxic gases like carbon monoxide in coal mines before it affects humans. In cybersecurity, canaries (or canary tokens) play a similar role, helping defenders discover breaches early.

Canary tokens are an easy way to discover network and system intrusions. The token is essentially a file, URL, email address, DNS hostname or similar resource, and is conspicuously deployed in common network and system locations. When someone accesses the token, an alert is triggered and the token owner is notified. The tokens may be inadvertently triggered too, but such occurrences can be reduced by the strategic placement of tokens, and general awareness among the defenders. Of course, if you are looking to guard against malicious insiders, you'll want to keep the knowledge of tokens to a minimum.
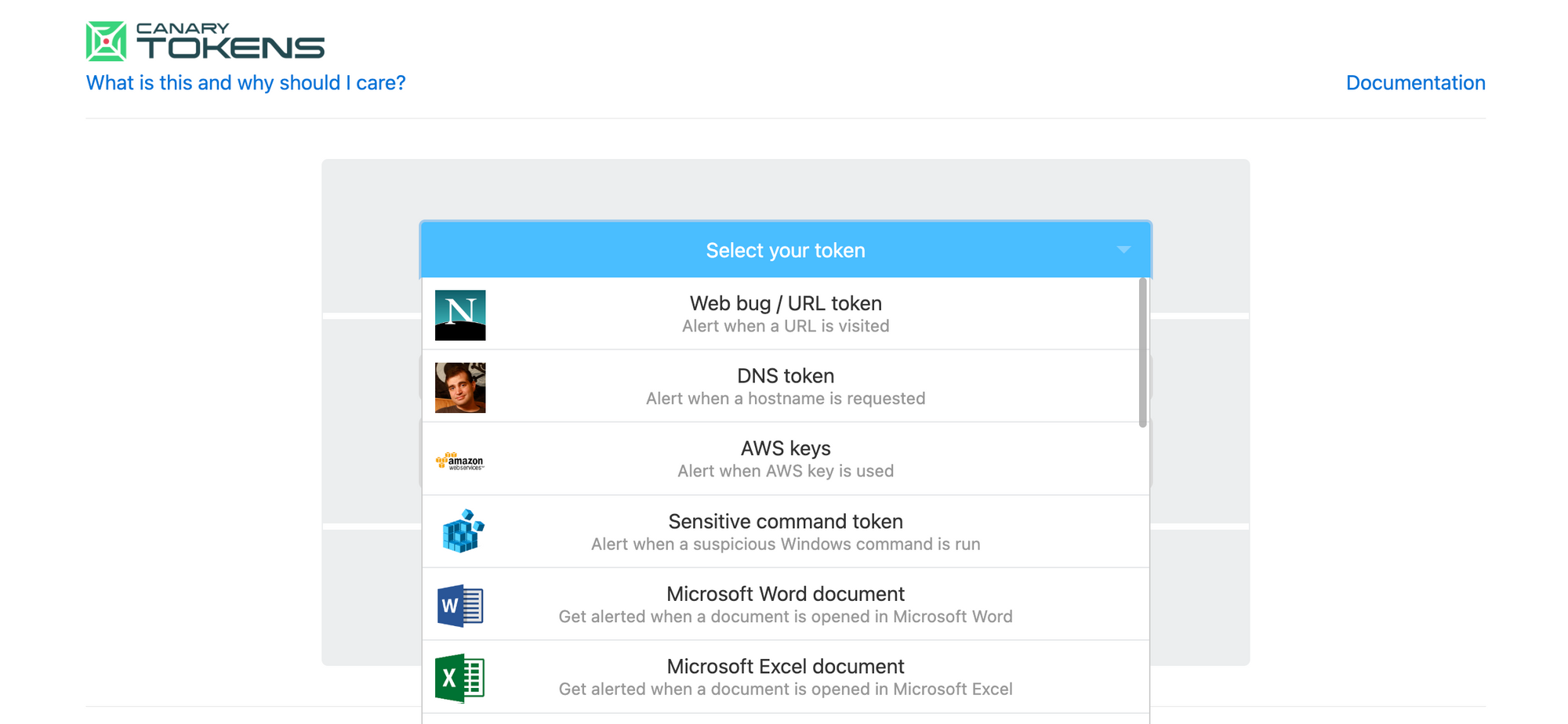
While canary tokens are not difficult to set up, Thinkst has made it really easy by running a self-service portal. You can create a variety of tokens, and have the alert sent to an email address of your choice. This service is based on their open source canarytokens project, which I'll cover in a separate post.
Canary tokens are similar in objective to honeypots - both look to deceive attackers into accessing them. Honeypots have a broader scope though, offering complete environments that mimic real-world resources, within which attacker movement can be tracked and their behaviour can be studied. Honeypots have traditionally been difficult to manage and scale, and open source honeypots have rarely taken off in enterprise environments. Canary tokens are easier to deploy, and may lead to a wider adoption in times to come.